We always see computers left unattended and unlocked at the workplace and even worse, public places like coffee shops. In Windows Creators update, Microsoft has introduced Dynamic Lock. When you pair your phone (Bluetooth) with Windows 10, now the option to lock the computer automatically when you walk away will be available.
If you have the Insiders Preview today, you can test this by enabling Dynamic Lock by going to Settings > Accounts > Sign-in options and toggle Dynamic lock to “on”. Make sure you phone is paired to your computer first.
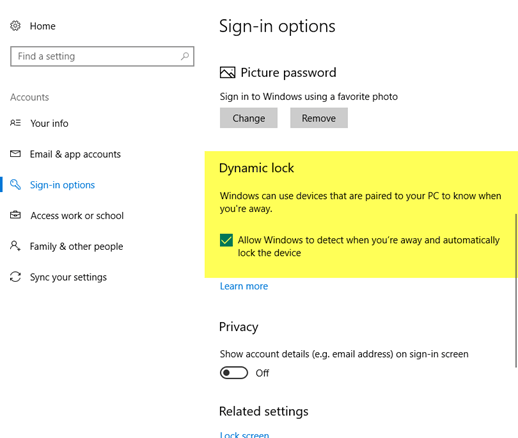
For the Enterprise, Dynamic Lock can also be enforced via Group Policy.